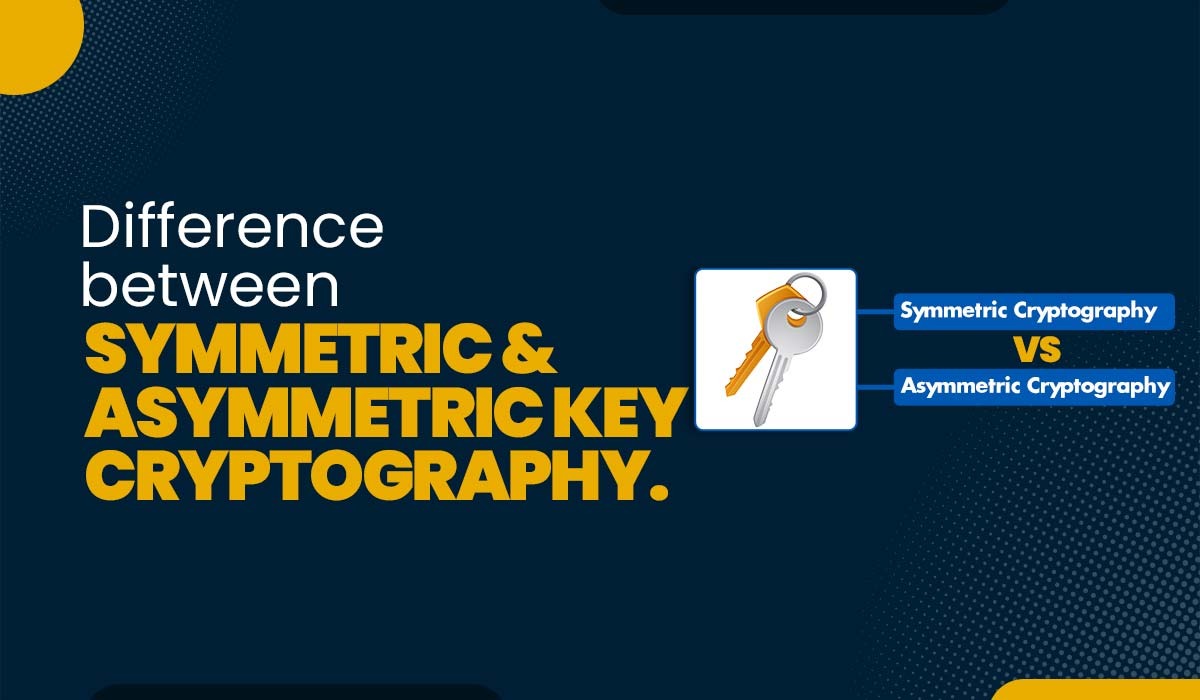
Introduction Scammers and other cyber criminals are getting more active in today’s society, harming millions of consumers. It is essential to encrypt everything to stop these people from stealing priceless data. Fortunately, three alternative encryption techniques may be used: symmetric encryption, asymmetric encryption, and hash functions (Keyless). In this blog, we will be mainly focusing […]
Read More
Introduction A thorough understanding of network structure and devices is essential for network engineers and administrators. The devices that are part of a network as well as the interfaces, protocols, and settings each one uses, must all be understood. This data may help with troubleshooting, boost performance, and keep the network safe. But where may […]
Read More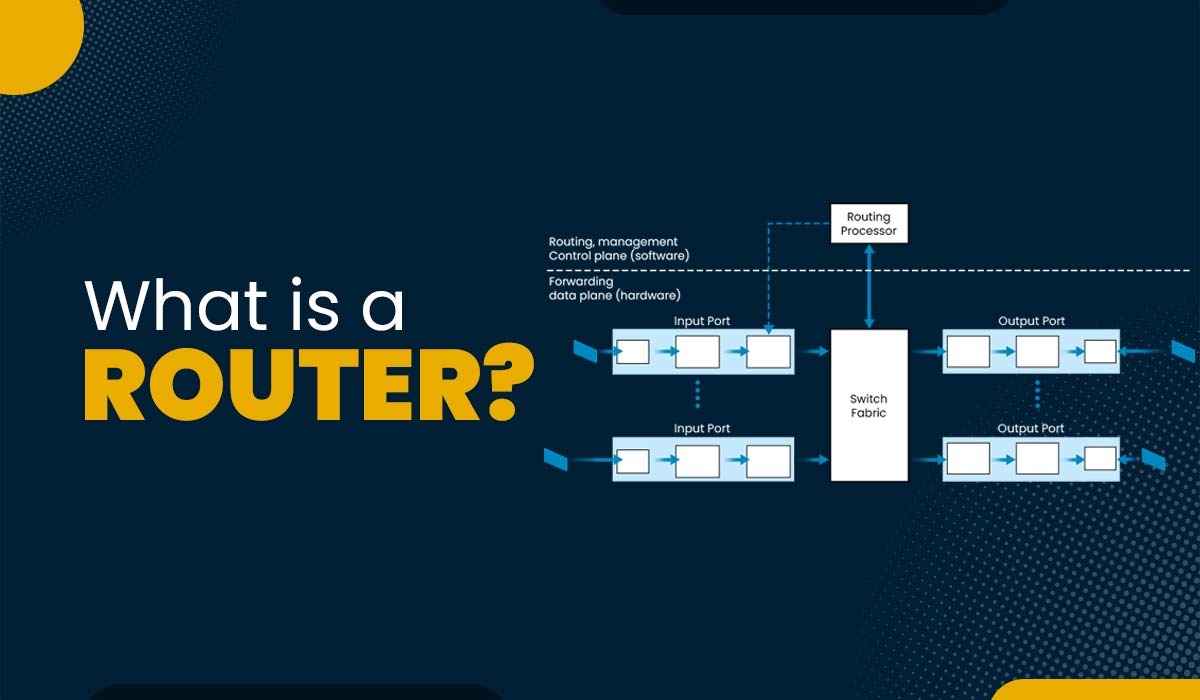
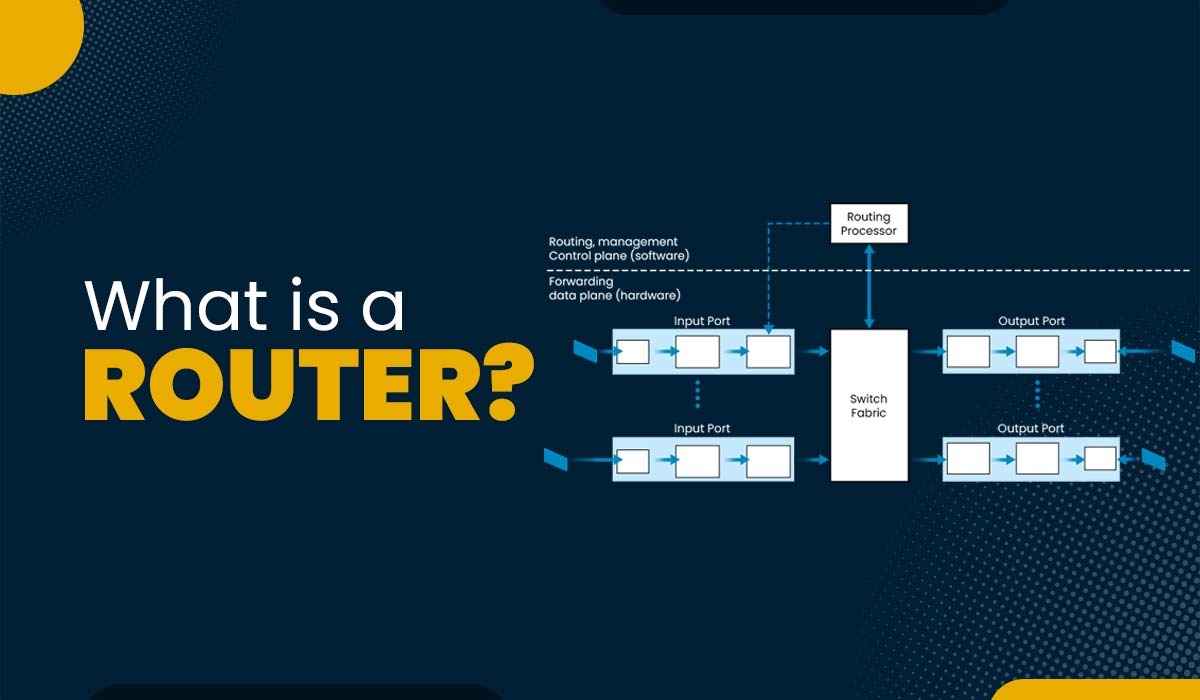
Introduction Data can be found anywhere nowadays. We use it for work, study, fun, and communication. But how is information delivered between devices? How can we guarantee the security and dependability of our data? Routers are the solution. A router in computer network is a component that connects various networks and routes data packets to […]
Read More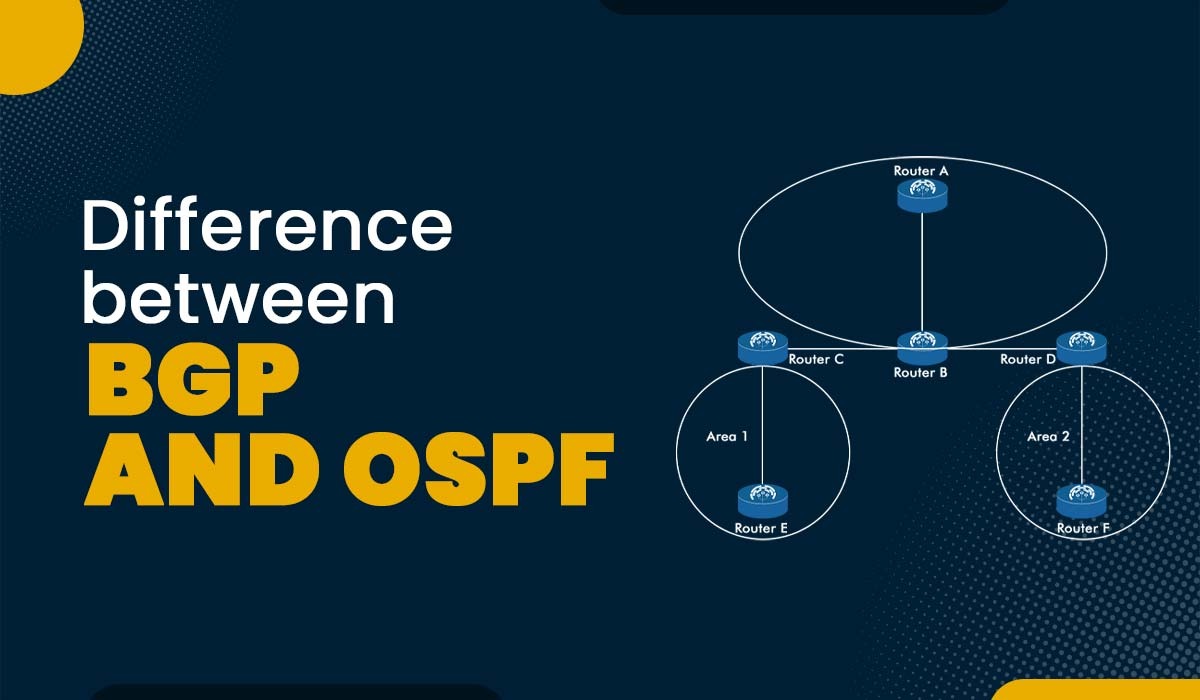
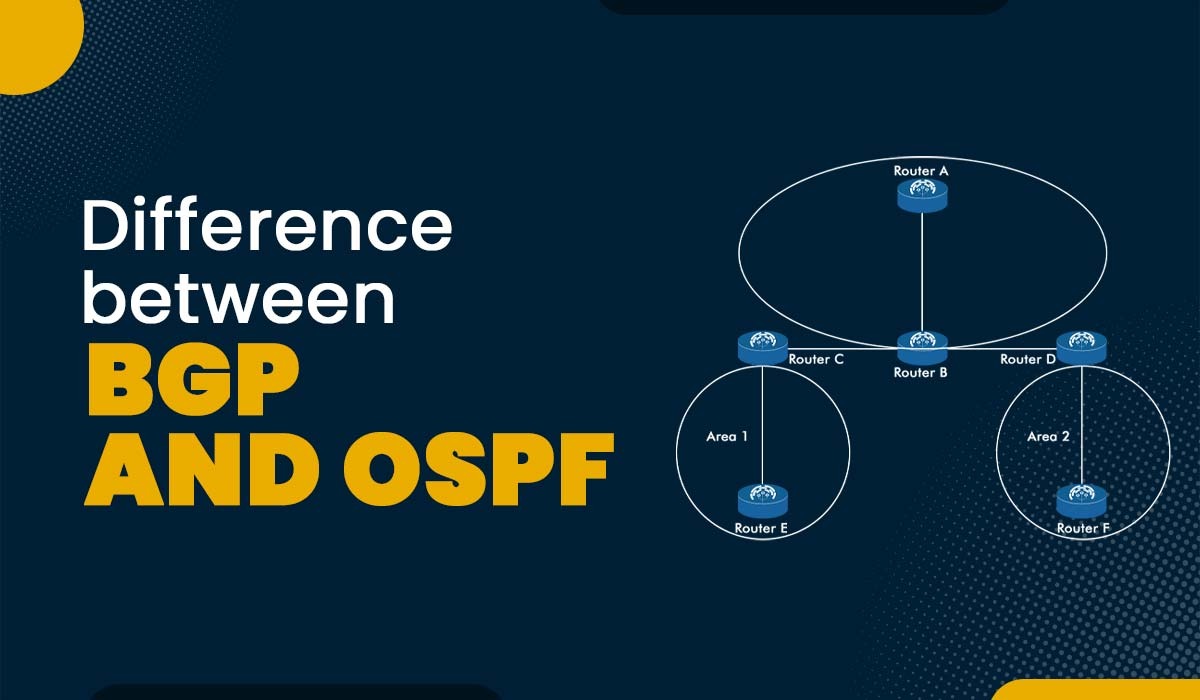
Introduction Using routing protocols, routers may automatically and dynamically exchange routing data. As each routing protocol has been developed to be ideally suited to a certain network implementation situation, there are several routing protocols to select from, each with its own advantages and disadvantages. Open Shortest Path First (OSPF) and Border Gateway Protocol (BGP) are […]
Read More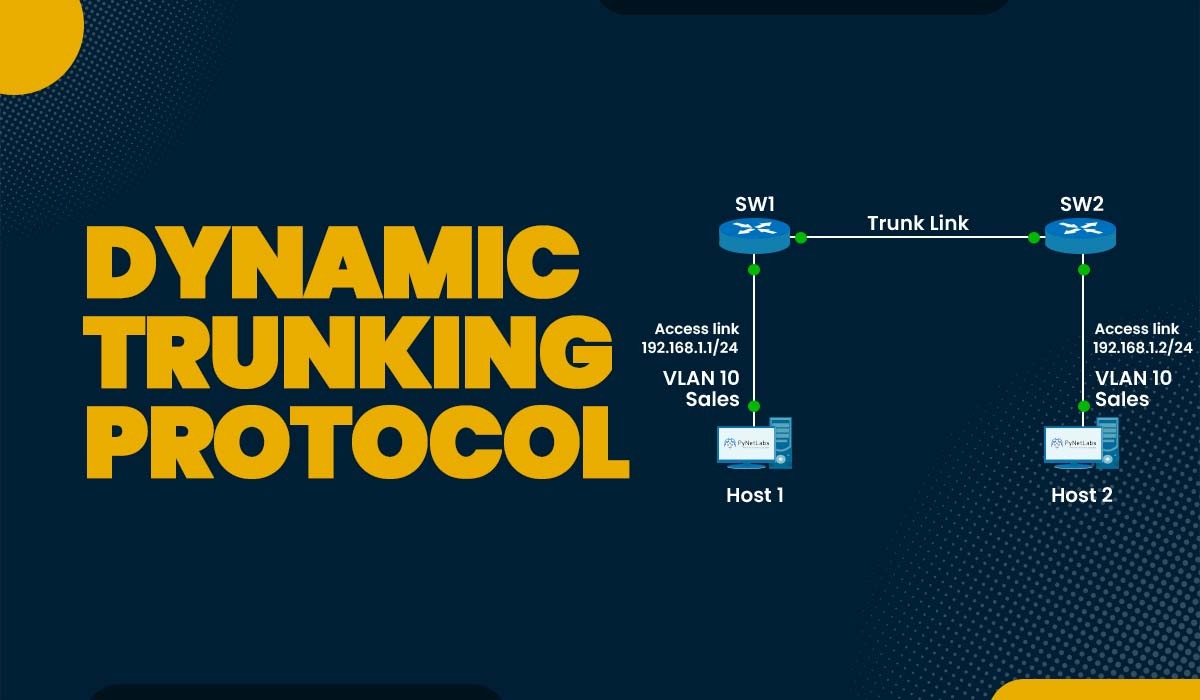
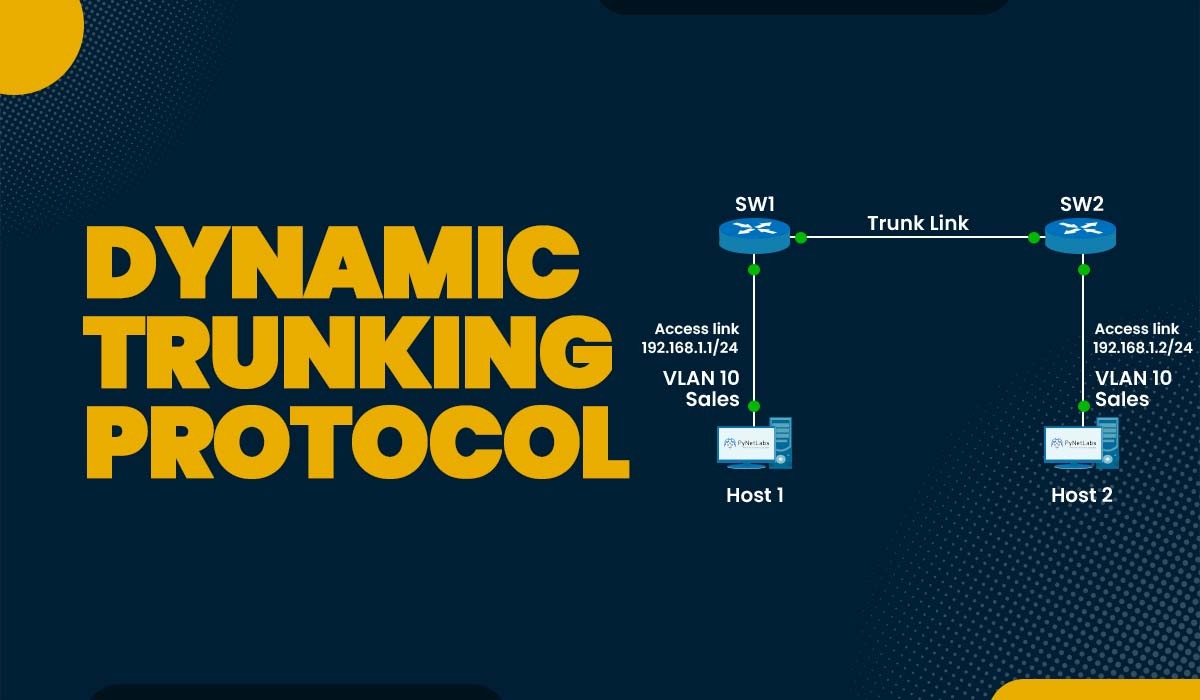
Introduction The word trunking may be familiar to network engineers or students studying networking. Multiple VLANs (virtual LANs) may share the same physical connection between switches using the practice known as trunking. With this method, you may separate various traffic types for security and performance reasons while conserving ports, cables, and bandwidth. But how do […]
Read More
Introduction Nowadays, everyone relies heavily on digital platforms, whether for business purposes or some important transactions. With the increase in digital presence, protecting personal data from hackers is crucial. VPN in cyber security is one approach to stop third parties from obtaining vital data for their benefit. In this blog, we will discuss what a […]
Read More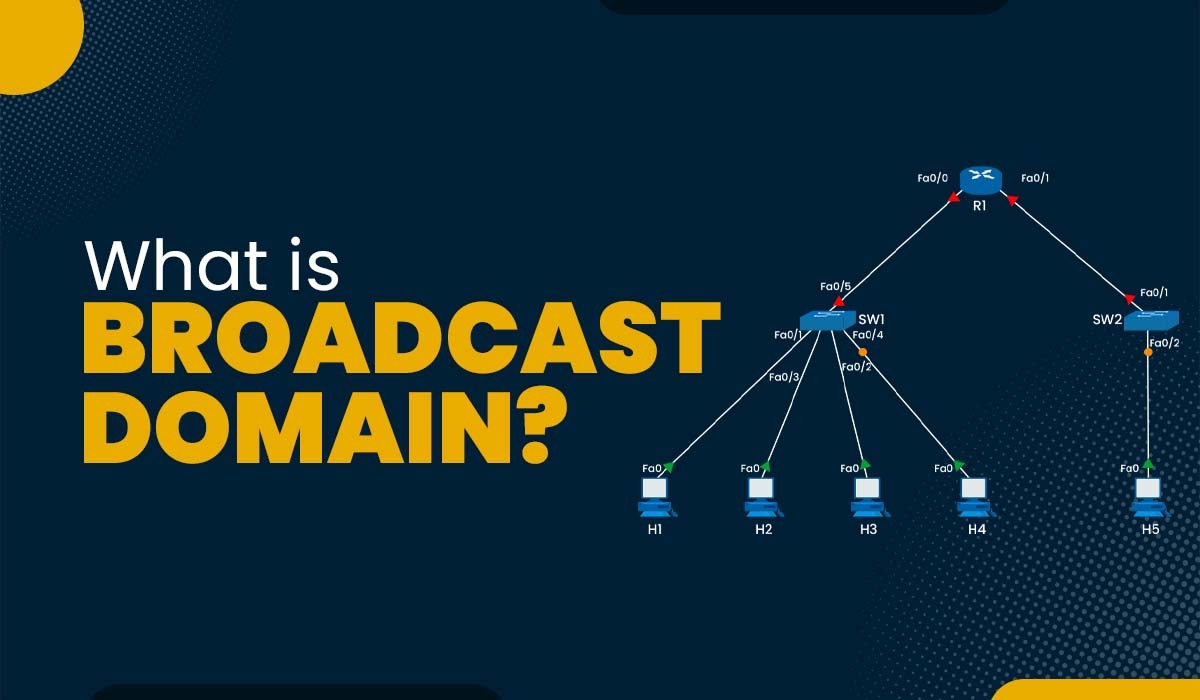
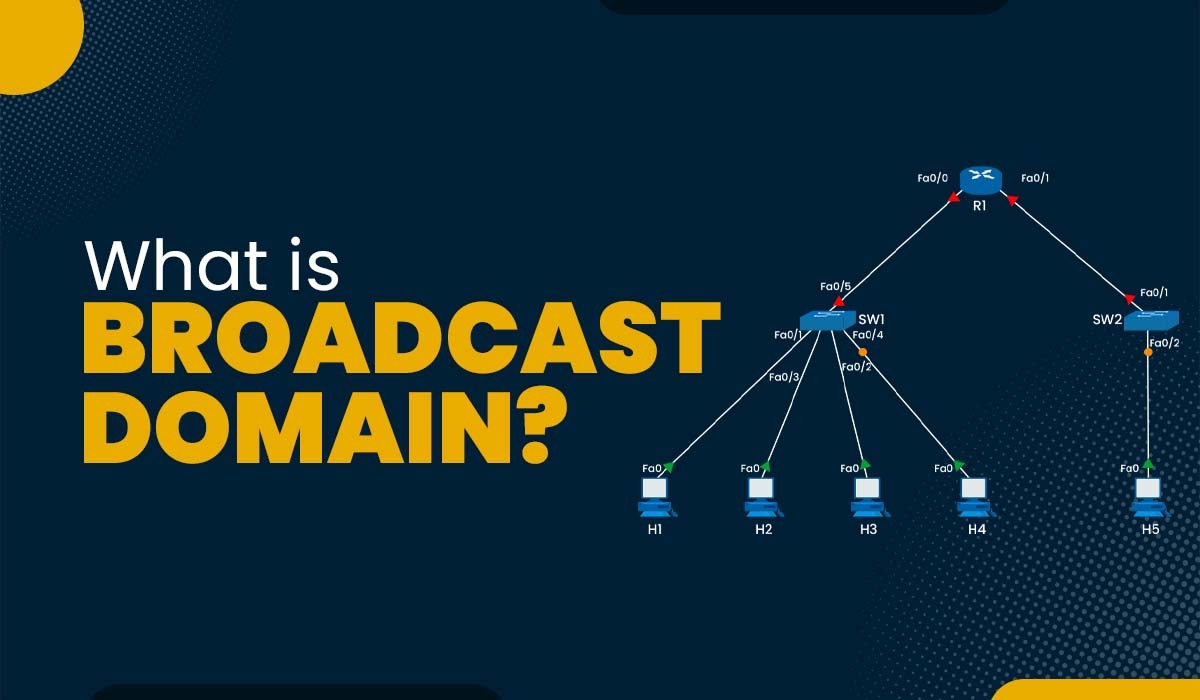
Introduction The study of networking covers a wide range of topics and technologies. A logical subdivision of a computer network where all nodes may interact with one another by sending and receiving broadcast messages is known as the broadcast domain. Regardless of their destination address, broadcast messages are unique data packet types distributed to all […]
Read More
Introduction Networking is now crucial to the success of almost every business in the modern digital environment. The importance of understanding how VLAN and Subnet function has grown as networks have expanded in both complexity and size. In this blog, we will explain the basic difference, i.e., VLAN vs Subnet, that will assist in understanding […]
Read More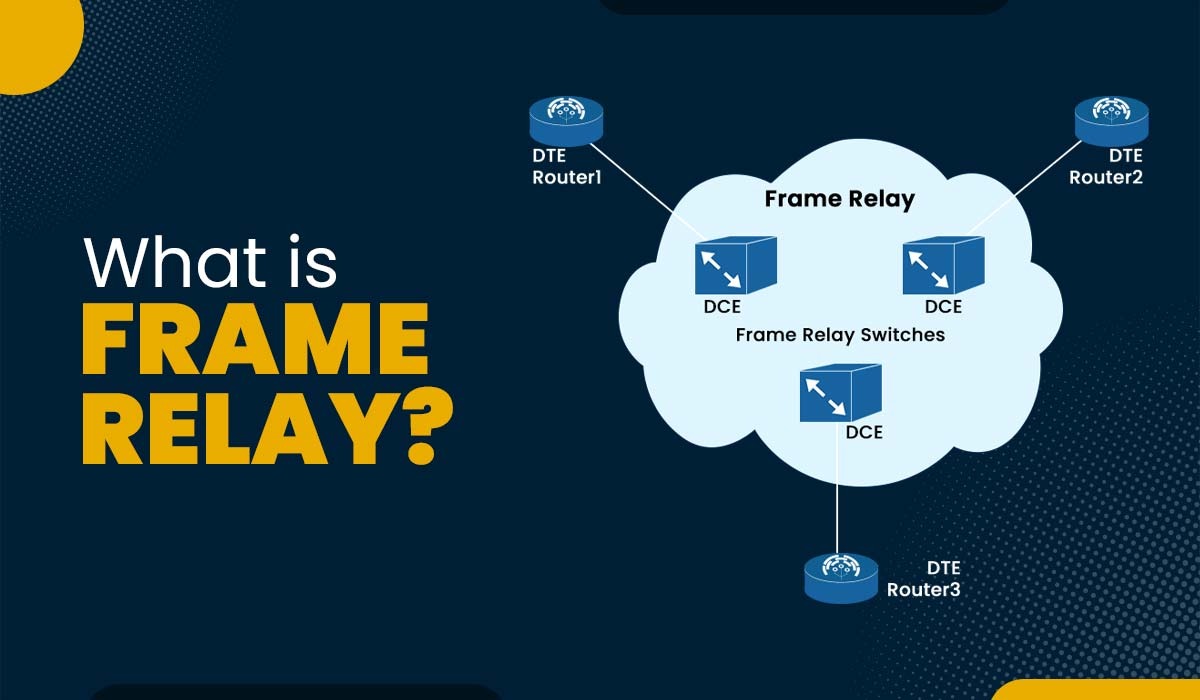
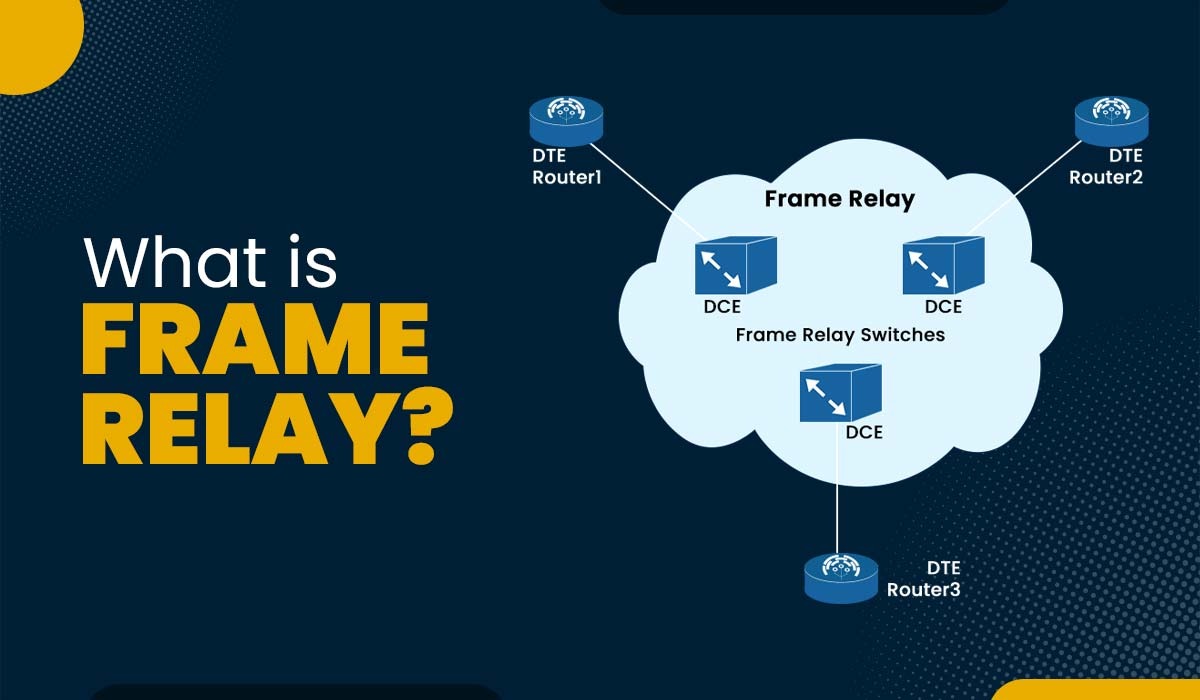
Introduction In computer networks, data communication is crucial for many applications as well as services. Data communication is the data transmission process over a network between multiple devices. It is important to note that various devices support different data formats, transmission speeds, and protocols. Hence, there is a need for a common network technology that […]
Read More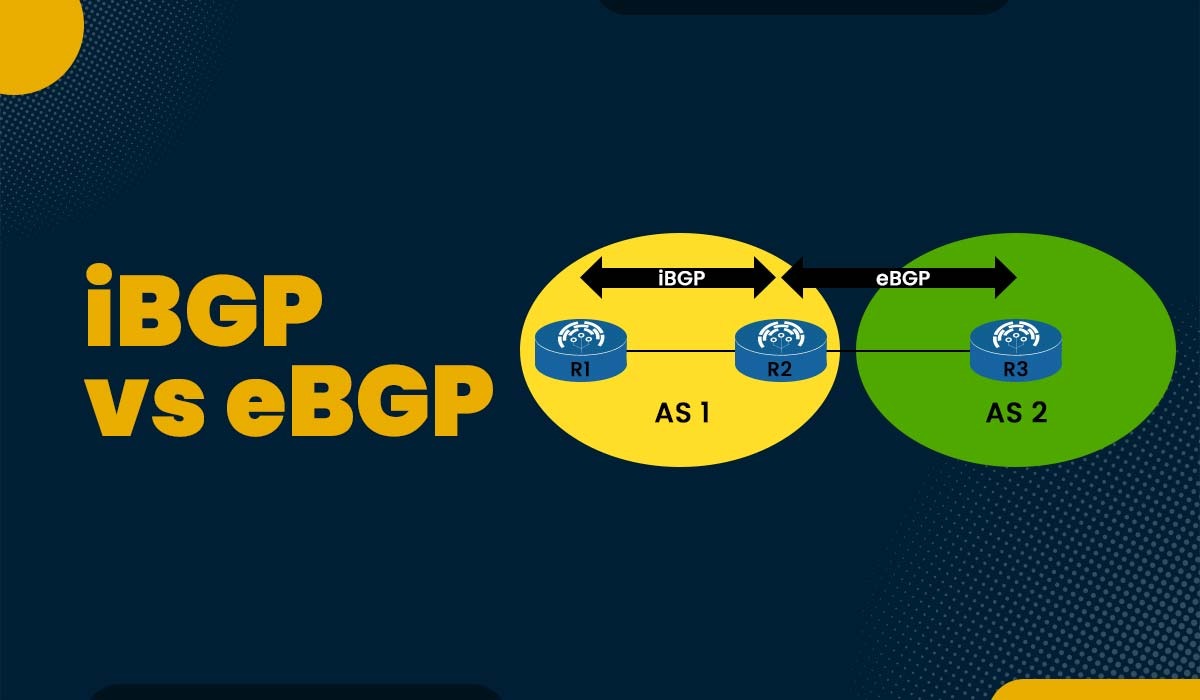
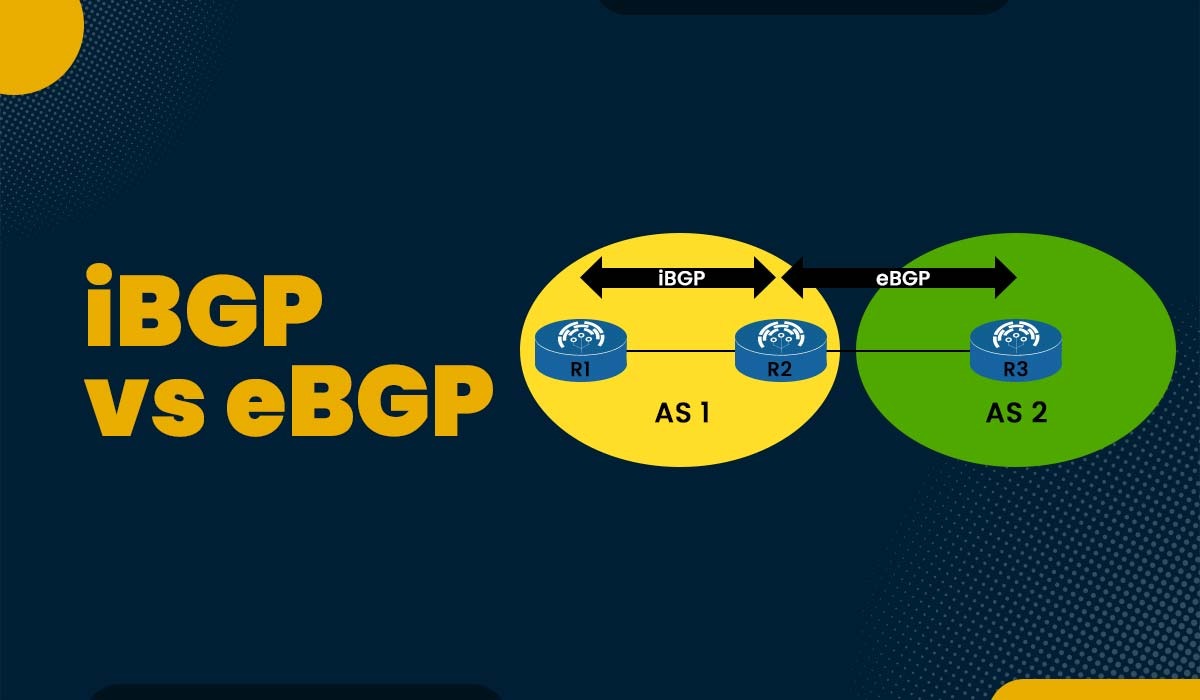
Introduction One of the foundations of modern networking is the border gateway protocol or BGP. Without BGP working in the background to allow system communication, the modern internet as it is known today would not be able to operate. The routing protocol known as BGP has two different versions, i.e., eBGP and iBGP. Both provide […]
Read More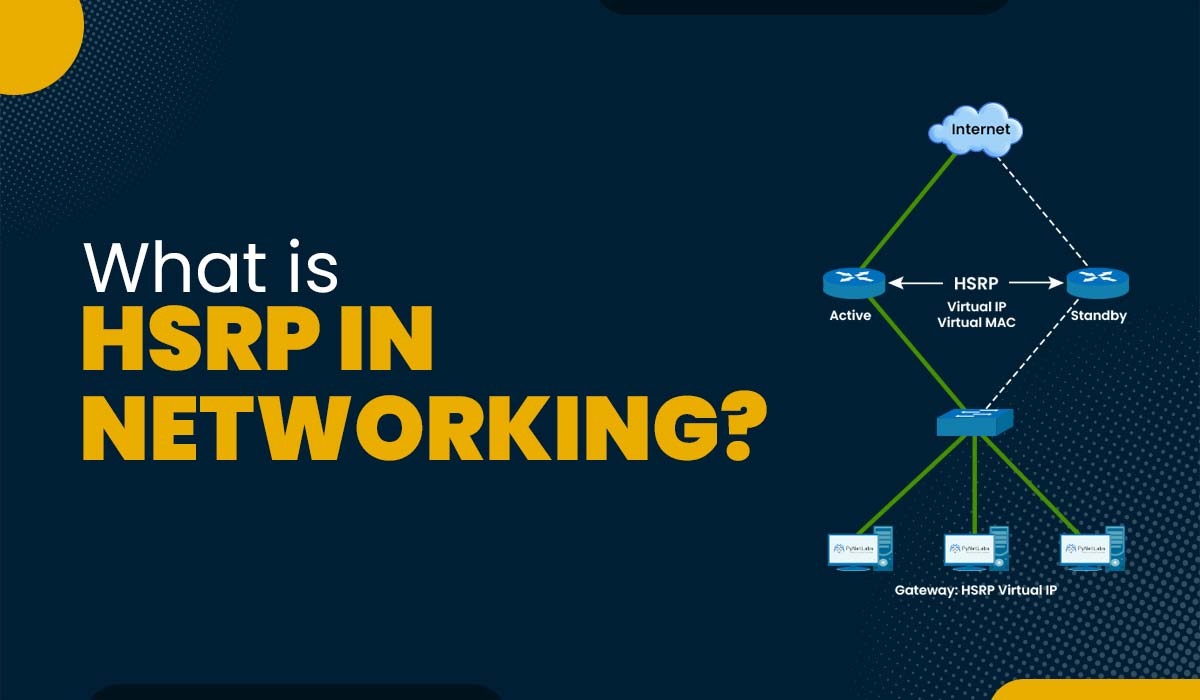
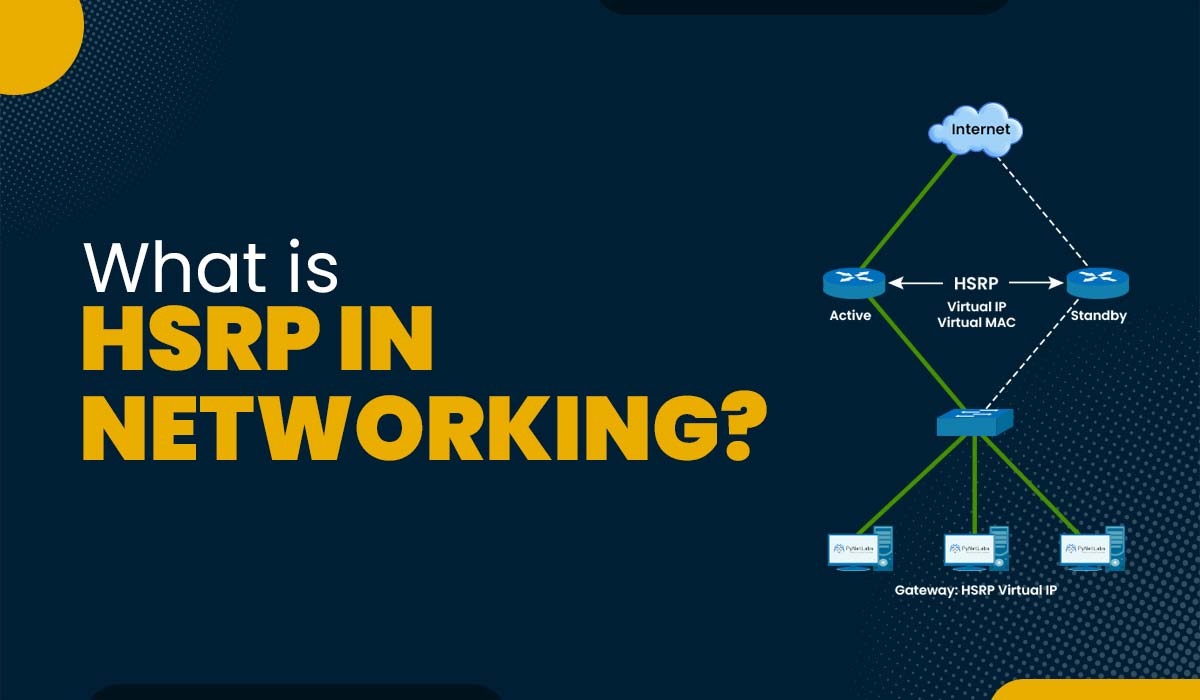
Introduction Redundancy is a crucial component of every modern network. In this digital era, staying without a network for even a short time is hard. You should include some redundancy if you don’t want your firm to cease operating. All of your devices will stop communicating with the outside world if the default gateway fails […]
Read More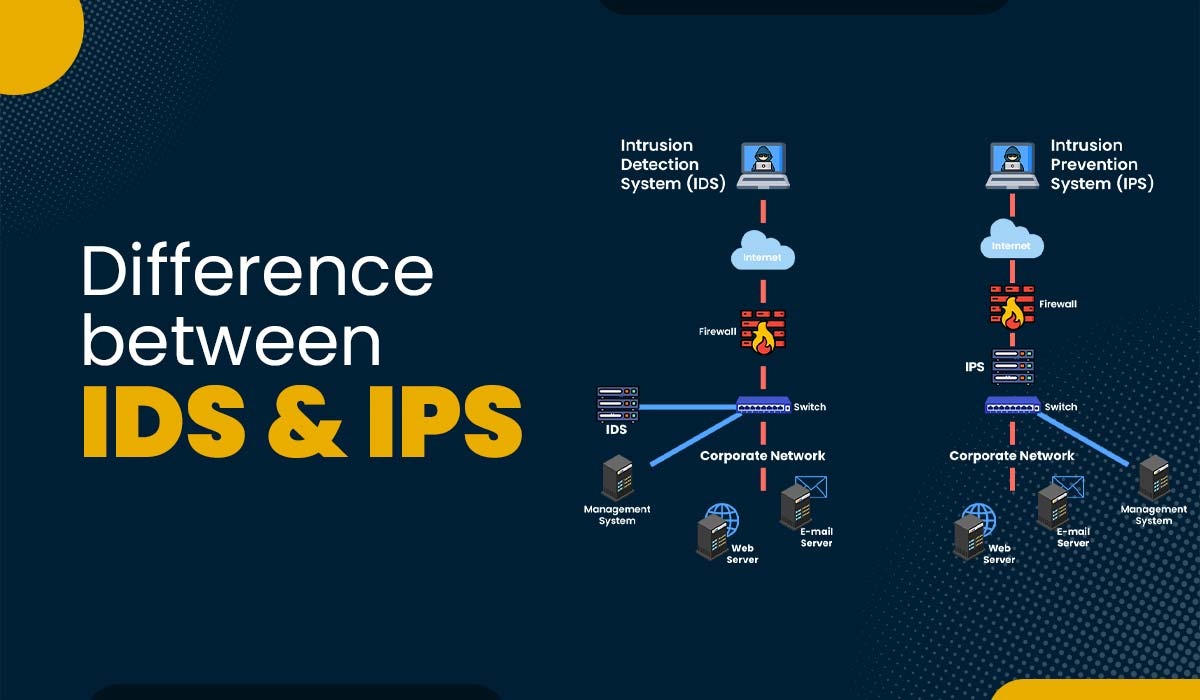
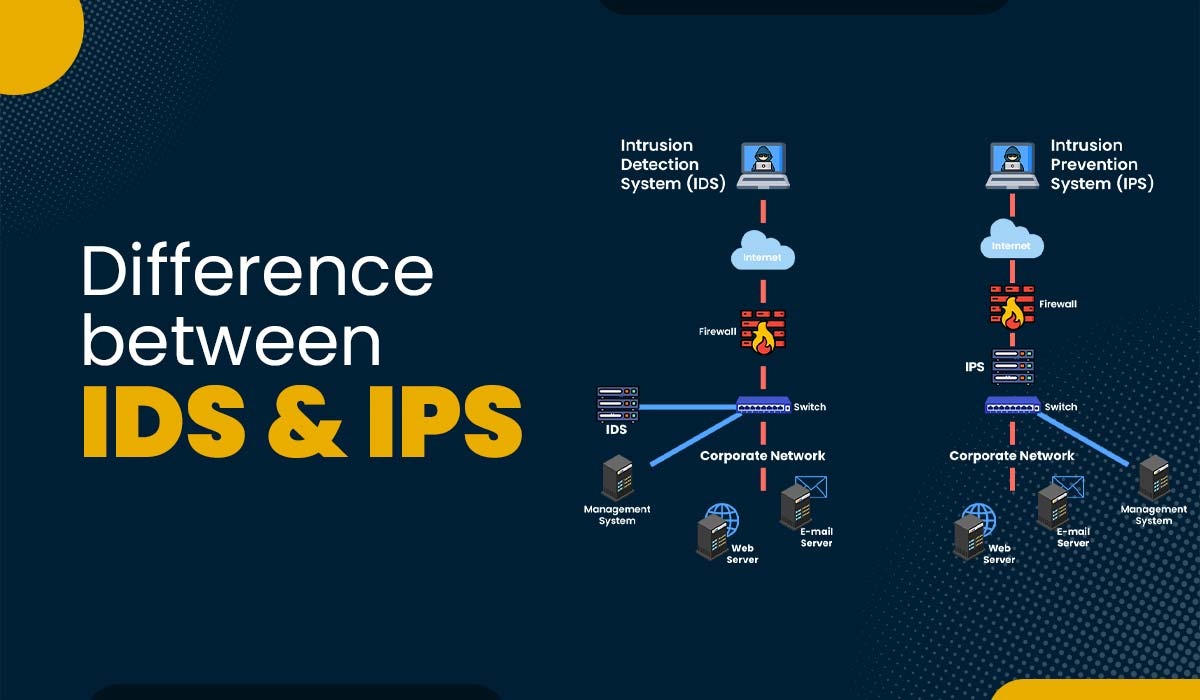
Introduction Nowadays, attackers’ knowledge and sophistication level is increasing steadily, making a single defensive method against intruders insufficient in providing substantial security. Instead, organizations should prioritize implementing a comprehensive and multi-layered strategy that combines proactive and defensive measures to safeguard their network and assets from unauthorized individuals. That’s where IDS, IPS, and firewalls come into […]
Read More